Why an AI Fintech Platform Is a Uniquely High-Risk Environment
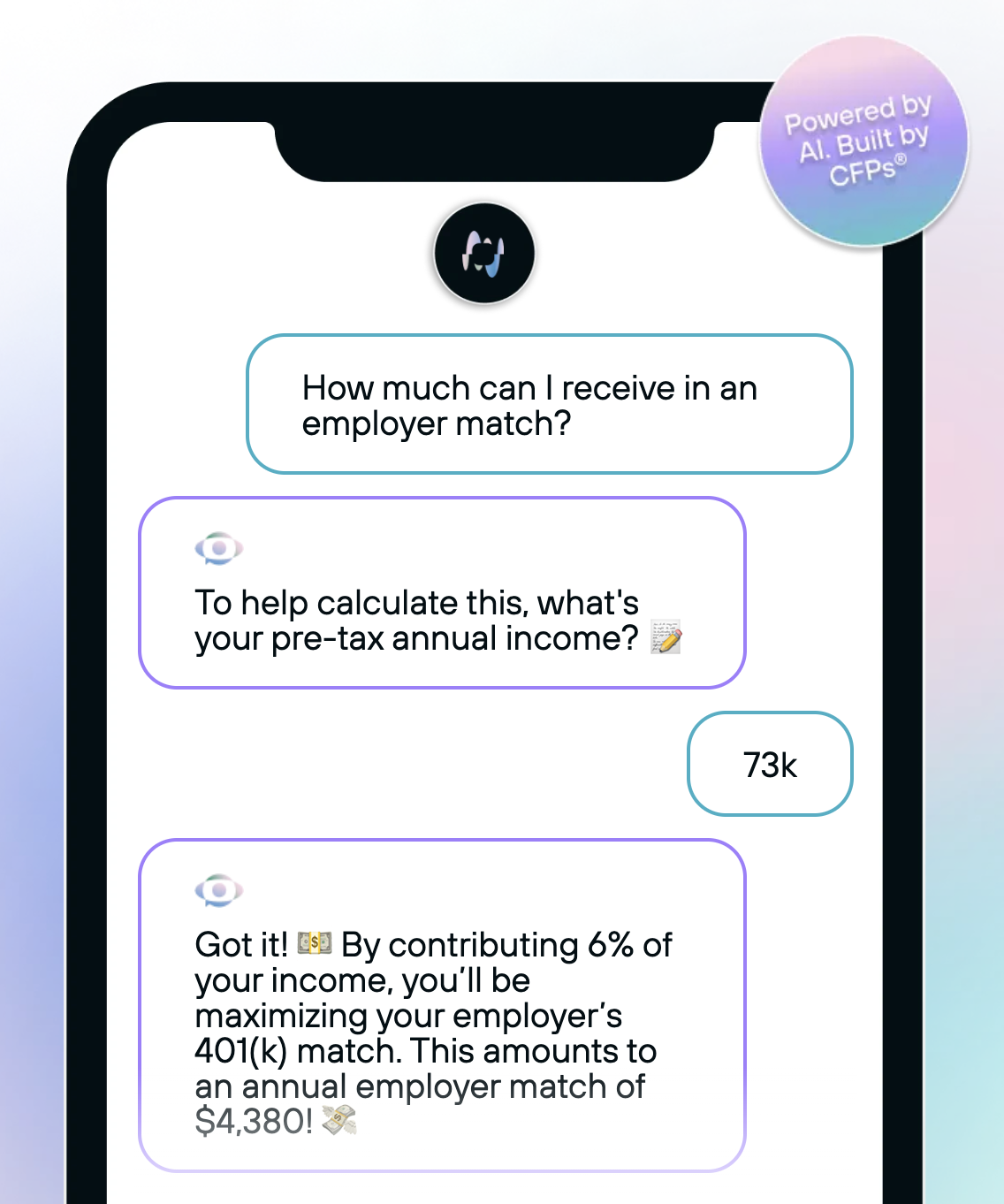
MasterFi isn't a chatbot. It's a financial advisory system that ingests deeply personal data - income, debt balances, 401(k) contributions, credit card APRs, retirement projections, employer benefit structures - and processes it through AI models to deliver personalized financial guidance via consumer messaging platforms.
That architecture creates a threat surface most startups don't understand until it's too late.
Key KPIs:
Fly.io → AWS Infrastructure Migration Benchmarked is architecting and executing MasterFi's migration from Fly.io to AWS - delivering enterprise-grade infrastructure with proper environment separation, access governance, PII isolation, and a baseline architecture for SOC 2 Type 1 certification.
4–6 Days Migration Estimate The full migration scope - AWS setup, component deployment, environment separation, access governance, PII database isolation, and team onboarding - scoped and estimated at 4–6 man-days. Speed without shortcuts.
SOC 2 Baseline Built Into the Architecture Every infrastructure decision - from database segmentation to access controls to encryption policy - is designed with SOC 2 Type 1 requirements in mind. Compliance isn't a retrofit. It's the foundation.